Hello coders!! In this article, we will be learning about python sha256. We will understand its meaning, its purpose and will also learn its implementation. So let us dig into the topic.
What is Python SHA256?
SHA stands for Secure Hash Algorithms. These are set of cryptographic hash functions. These functions can be used for various applications like passwords etc. The hashlib module of Python is used to implement a common interface to many different secure hash and message digest algorithms. The hash algorithms included in this module are:
- SHA1: a 160-bit hash function that resembles MD5 hash
- SHA224: internal block size of 32 bits (truncated version)
- SHA256: internal block size of 32 bits
- SHA384: internal block size of 32 bits (truncated version)
- SHA512: internal block size of 64 bits
- MD5 algorithm
Different functions associated with Python sha256:
- encode(): used to convert the string into bytes
- hexdigest(): used to return the encoded data in hexadecimal format
Implementation of Python sha256:
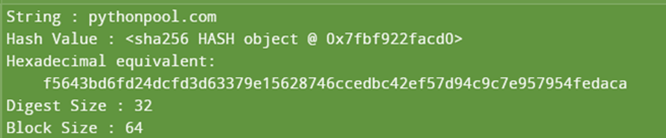
import hashlib
string="pythonpool.com"
encoded=string.encode()
result = hashlib.sha256(encoded)
print("String : ", end ="")
print(string)
print("Hash Value : ", end ="")
print(result)
print("Hexadecimal equivalent: ",result.hexdigest())
print("Digest Size : ", end ="")
print(result.digest_size)
print("Block Size : ", end ="")
print(result.block_size)
Output:
Module Functions
Let us understand the various methods used in the above code:
Hashlib:
A Python module is used to implement a common interface to many different secure hash and message digest algorithms.
string.encode()
This function converts the string into bytes
Syntax:
string.encode(encoding=encoding, errors=errors)
Parameter Values:
- encoding: type of encoding that will be used
- Default value: UTF – 8
- errors: error method like backslashreplace, namereplace etc
hashlib.sha256():
This function is used to create a SHA-256 hash object.
Hexidiest():
This function is used to return the encoded data in hexadecimal format.
Python hmac sha256:
HMAC stands for keyed-hash message authentication code.
It is a type of message authentication code, that includes a cryptographic hash function along with a secret cryptographic key.
Syntax:
hmac.new(key, msg=None, digestmod='')
Parameters:
- key: secret key
- msg: If this is present, the update(msg) method is called.
- digestmod: digest name
Return Value:
A new hmac object.
import hmac
import hashlib
import binascii
def signature(key, msg):
key = binascii.unhexlify(key)
msg = msg.encode()
return hmac.new(key, msg, hashlib.sha256).hexdigest().upper()
print(signature("E49756B4C8FAB4E48222A3E7F3B97CC3", "Python Pool"))
Output:
519F46535F78F67235F27BC2C1155571C4A76F21A8FCD05B1918E1738F0F54CC
In this example, we have passed the secret key and the message to the signature() method. We converted the key into binary data using the binascii() method. Then lastly using the hmac.new() method, we generated the hmac object.
Python sha256 Encoding on a file:
In order to hash a given file in Python, we start reading it bit-by-bit. We keep the instances of the current hashing functions updated. Once the hashing function gets all bytes in order, we can then get the hex digest.
import hashlib
filename = "sample.py"
with open(filename,"rb") as f:
bytes = f.read()
hash = hashlib.sha256(bytes).hexdigest();
print(hash)
Output:
5f12568f6f0af1ec7a7ae7c69711215bcf312e1cfaf7b11b05af109b620ef21a
In this example, we have iterated through the file using a loop. We read every byte of the file and convert it into hash using the hexidigest() method.
Advantages of Python sha256:
- 64-byte block size indicator
- 33 byte of maximum message length
- 4-byte standard word size.
- 32-byte internal position length
- 64 iterations in one cycle
- Approx 140 Mib/s speed achieved by the[is Protocol
Application:
Python Sha256 is used in some of the most popular encryption and authentication protocols like:
- SSL: secure sockets layer
- TLS: transport layer security
- IPsec: internet protocol security
- SSH: secure shell
Sha256 is also used in unix and linux for password securing using hash.
Conclusion:
With this, we come to an end with this article. We learned about Python sha256, its meaning, and its implementation. We also saw the advantages and application of hsa256 in various security authentication protocols.
However, if you have any doubts or questions, do let me know in the comment section below. I will try to help you as soon as possible.
Happy Pythoning!
Thanks for the explanation, how do I put this into use?
It depends on your use case. Some people use it to encrypt passwords, while some use it to create authentication protocols.
Hello how can i decrypt an encrypted text with sha256 i cant find anywhere
SHA256 is one-way hash function. You cannot decrypt the text.